Fedex Express Delivery Service Email Scam Examples Review
Well-known companies and brands are favorite targets for fraudsters. After all, it is much easier to get people's attention with the apply of a pop proper name, then scammers have more adventure of trapping a gullible user.
In this article, we will analyze phishing and malicious emails sent by fraudsters that claim to come from international delivery services. The almost popular of these are DHL (Germany), FedEx and United Package Service (USA), TNT (Netherlands). All of these companies are international, with millions of customers using branches in major countries all over the earth. They provide similar services, so scammers employ the aforementioned methods and techniques in their fraudulent mails.
The phishers' goals include:
- Theft of confidential data (banking company card credentials, logins and passwords from personal accounts), mainly with the help of fake web pages imitating official pages of the site. In a phishing set on users provides the fraudsters with their personal data past filling the fields on false sites or sending them via email.
- Installing diverse malicious programs on users' computers. These programs are used not merely to monitor user online activity and steal personal data, merely also to organize botnets to distribute spam and launch DDoS attacks.
Headings of fraudulent emails
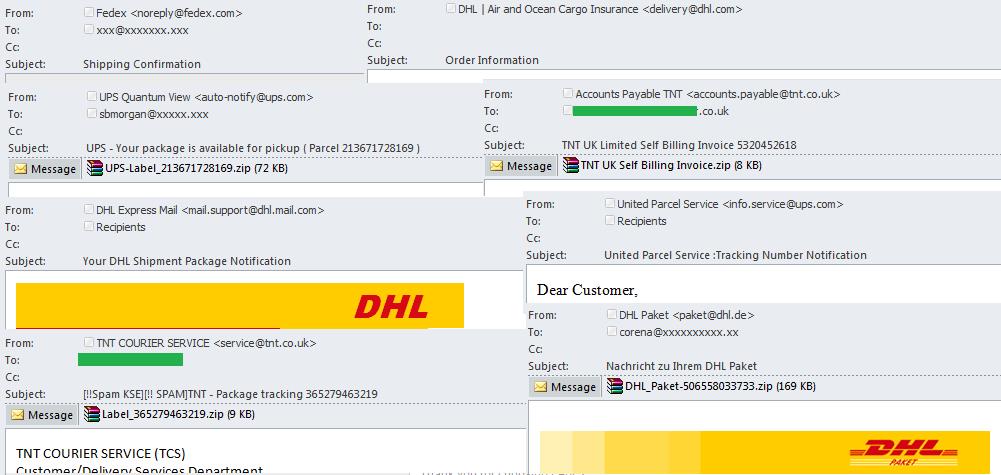
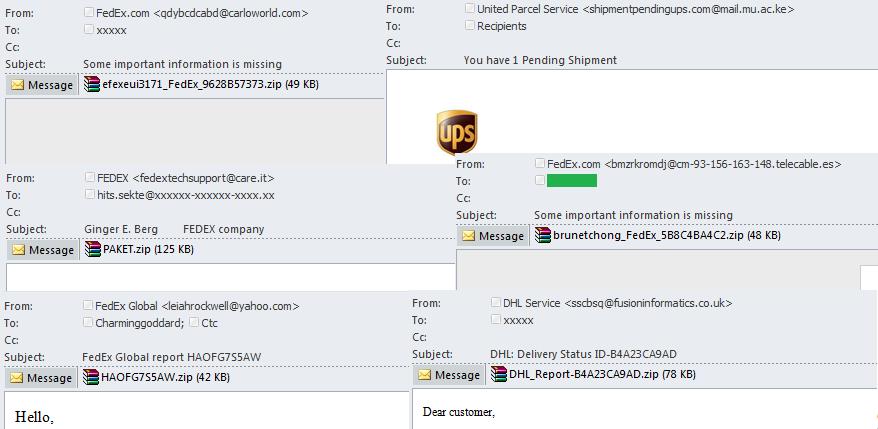
The From field
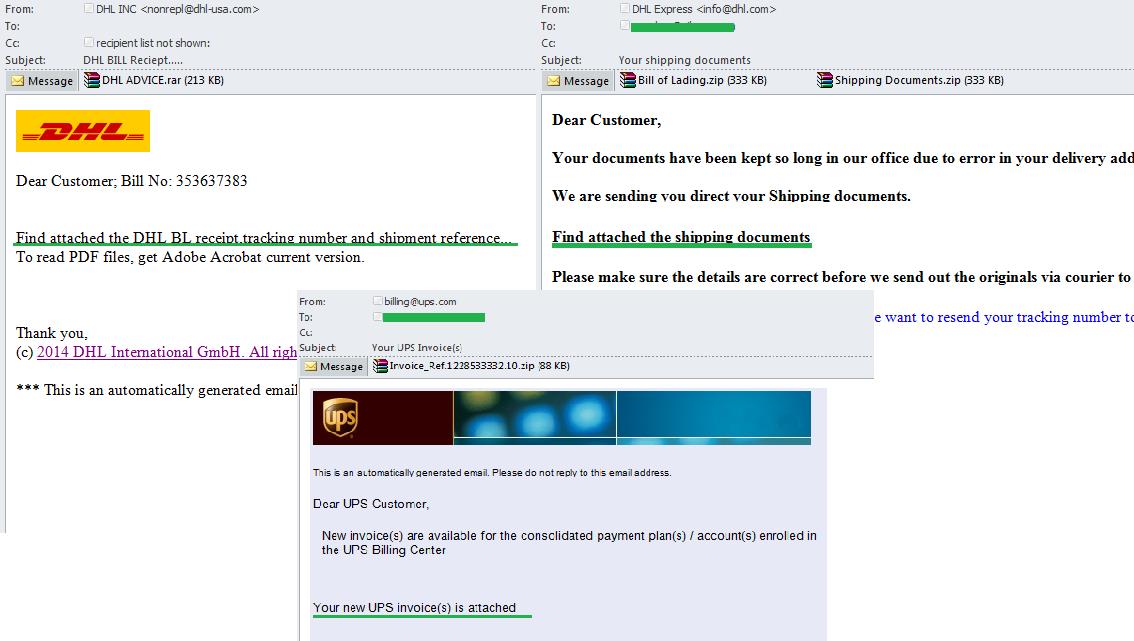
Structurally, the accost in the From field looks like this: Sender Name . To misfile recipients, scammers tin can alter parts of the address and oft make it look very similar to an official address of the delivery service.
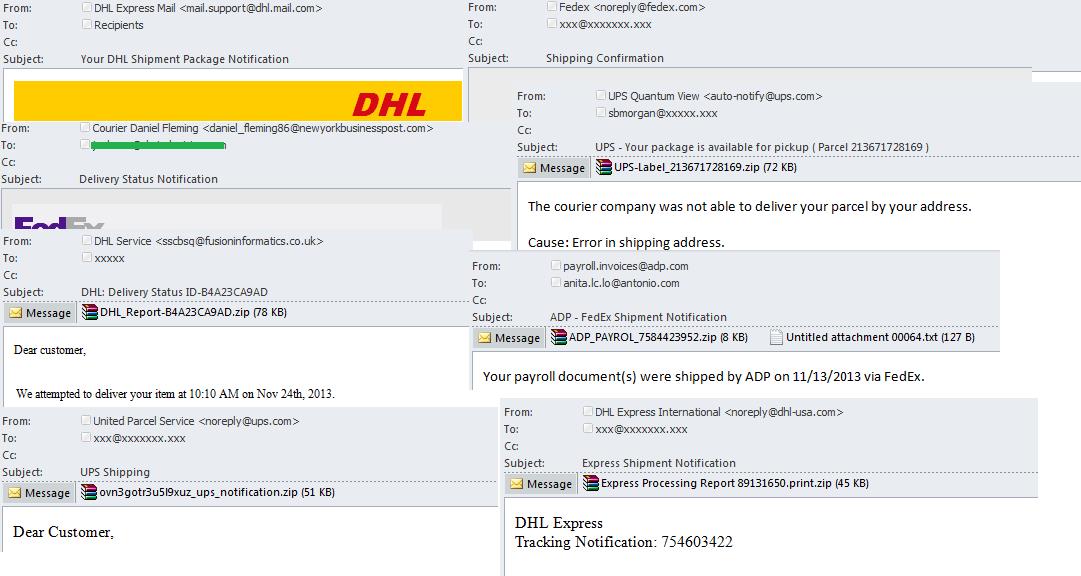
At that place are several groups of email addresses seen in fraudulent emails:
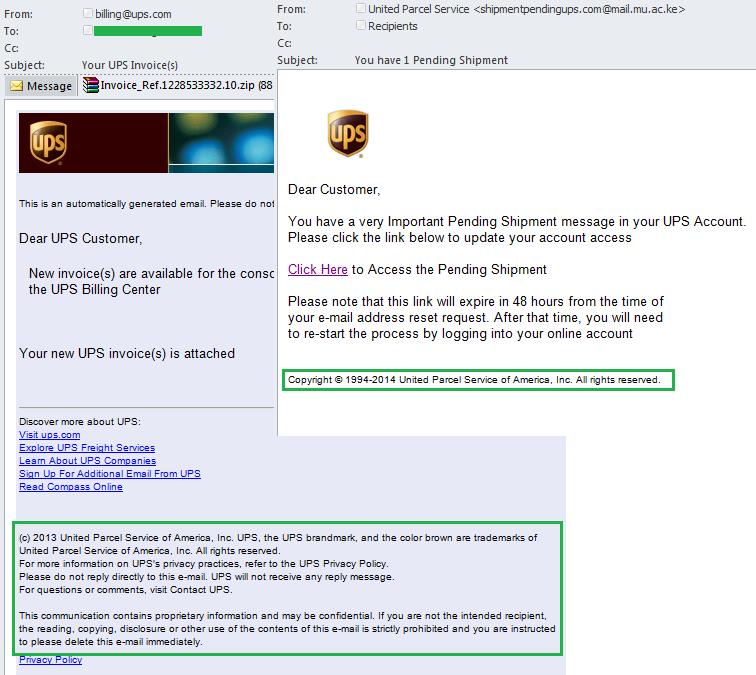
- Email addresses which closely resemble companies' legitimate public addresses. Mostly, they use the proper name of the visitor (DHL INC, TNT COURIER SERVICE, Fedex, etc.) every bit the sender name. The proper noun of the mailbox oftentimes includes the words info, service, noreply, mail, back up which are typical of email addresses used to send official notifications. The server domain name often has a real or very plausible company domain.
- Addresses which do non resemble legitimate company addresses. The sender name still reflects the company name (FedEx, DHL Service, FedEx.com) but the domain name commonly belongs to a costless email service or an admittedly different company. The email address could exist taken from a existent user (taken from public sources or hacked mailboxes) or automatically generated addresses. The latter unremarkably announced as a random sequence of letters, words and numbers.
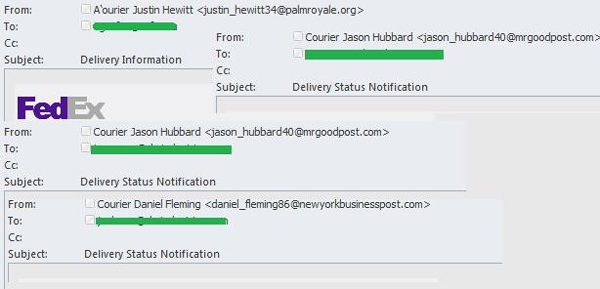
- Addresses that resemble e-mail service addresses of company employees. The sender proper noun may contain the name and surname of a supposed employee, or the company name, or a position (courier, managing director, etc). The name of the email box usually contains the same proper name and surname as the sender name because any difference in the data may alert the recipient to a fraudulent email. Either the existent visitor domain or other domains not related to delivery companies might be used equally a domain proper name.
- Addresses which but point the sender's address without a proper name.
While analyzing sender accost, remember that scammers practise not need to hack the company servers to use the real company domain in the From field. They tin can simply insert the necessary domain name of the server into the From field.
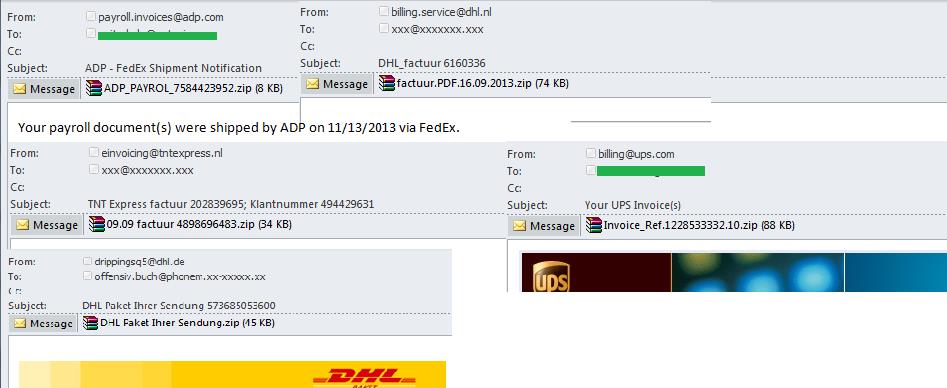
The Discipline field
The subject of the fraudulent post should capture the imagination of recipients and encourage them to open up the bulletin, just it likewise needs to be plausible. Therefore spammers choose mutual phrases typical of official notifications from delivery services. After sending a packet or a document, customers worry well-nigh its successful commitment and endeavour to follow its progress by reading whatever notification from a delivery service.
The most pop subjects are:
- Subjects related to the delivery/shipment (shipment notifications, delivery status, aircraft confirmation, shipment documents, delivery data, etc.).
- Subjects related to tracking shipments, order information and invoices (the tracking number of the shipment, tracking the shipment, etc.).
- Subjects related to notifications about messages and accounts (creation and confirmation of accounts, new messages, etc.).
Examples:
Examples:


The design of the email
Scammers pay special attention to the design of the email. Their main goal is to make message as believable as possible. After all, if it looks suspicious, a potential victim volition most probable delete it despite the attractive discipline and plausible sender address. Allow's analyze the basic techniques that fraudsters use to make emails expect legitimate.
Graphic design
All major international companies accept their ain corporate style, including wordmarks, graphic trademarks, corporate fonts, slogans and colour schemes. These are used on the official website, in mailings and commercials, and in other design components. Scammers use at least some of these elements when designing fraudulent emails to make them look convincing. Usually phishers focus on logos because these elements are unique to each company and is an immediate identifying mark.
Examples of DHL company logos used in fraudulent emails.
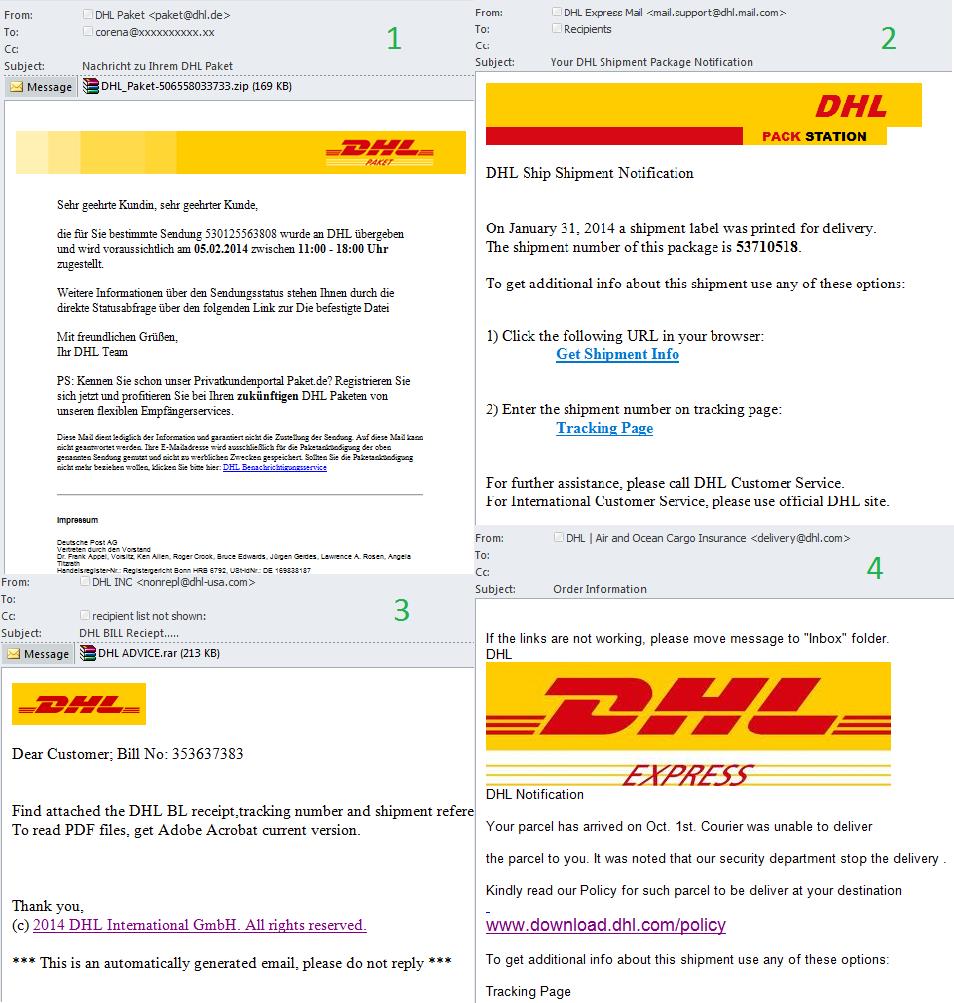
Let's have a closer look at these examples. It'due south immediately obvious that the second instance is very unlike from the company'south official logo. Some other sign of a forgery is the divergence in size between the false logo and the original, as seen in the quaternary example where the logo takes almost a third of the message. Here the plan is probably to attract the reader's attention with a big brilliant motion-picture show rather than apparently text. That as well explains why the phishing links announced in a larger font: users should respond to it immediately, without trying to read the small print.
In the first example, the scammers are trying to copy the design from the official site (a very pop method). However the logo is placed on the right-hand side rather than on the left. Also they are using a colour alloy for the logo background rather than making it unmarried-colour. The logo in the third case well-nigh closely imitates the original DHL logo: the scammers take tried to match its size and design. It'due south not really all that difficult to brand a logo for a fake notification: there are plenty of versions of the original image available online in several formats, including vector graphics. In improver to the logo the fraudsters apply the colour spectrum chosen by the company in its official resources and mailings. For instance, for DHL it is a combination of yellowish and red.
The text design
In most official emails we find a number of set phrases, specially when it comes to standard notifications generated and sent automatically. These letters oft include contacts and links to the official resources of the sender. Therefore, to make the text of the imitation email wait similar an original notification from a delivery service the fraudsters use:
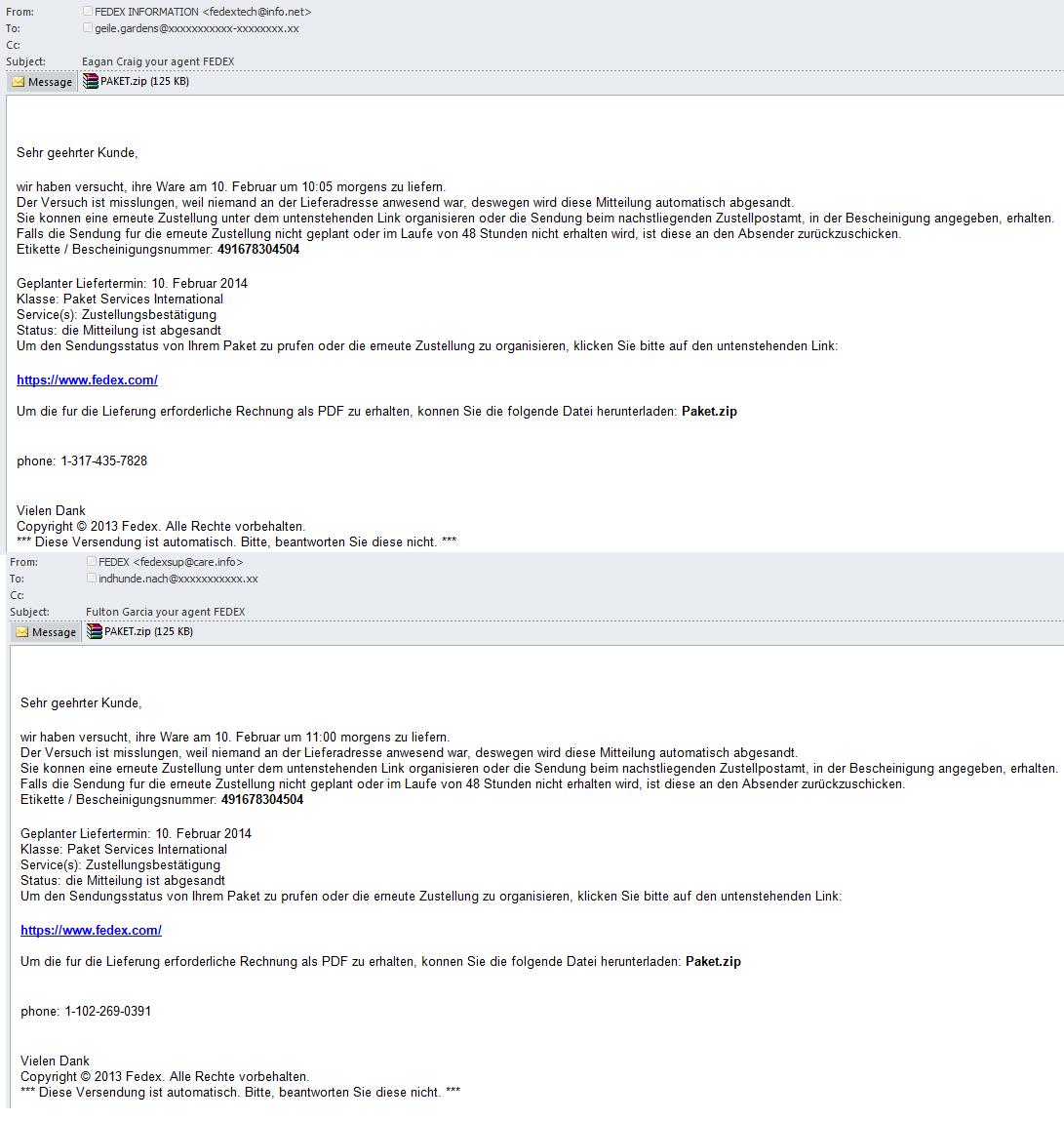
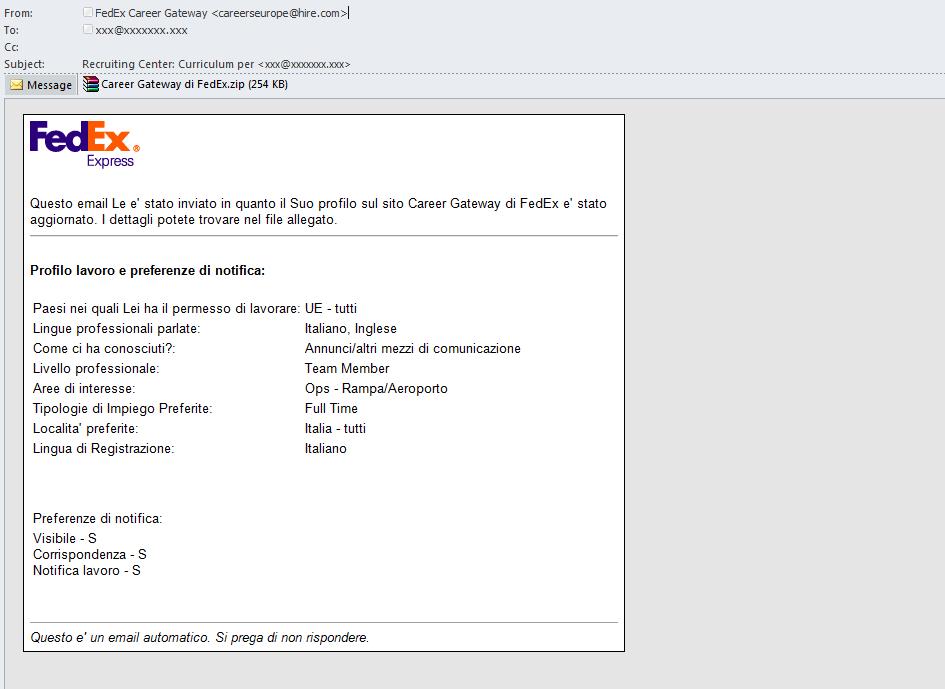
- Standard phrases typical of official mass mailings: Delight do non reply to this email, This is automatically generated email, please do non answer, All rights reserved, Diese Versendung ist automatisch, Bitte beantworten Sie diese nicht, This advice contains proprietary data and may be confidential. Questo e' united nations e-mail automatico, Si prega di non rispondere, etc.
- Links to the official page of the company. Not all links contained in the fraudulent electronic mail are phishing – spammers may besides utilise the links which really pb to the official resource on order to brand their emails look legitimate and featherbed spam filtering.
- Contact for feedback. The fraudsters frequently indicate the contact information of the sender or the company (proper noun, surname, position, role address). These contacts might be existent or fictitious.


The content of the email
When fraudsters transport out imitation emails disarming readers that information technology is a real message is but part of the battle. The next step is to persuade the potential victim to practise what the scammer requires, such every bit providing personal information or installing a malicious file. This is where psychology comes into play, and the electronic mail content is the main tool.
In fraudulent notifications allegedly sent on behalf of delivery services frequently employ the following tricks:
- Notifications of various problems (eg. unsuccessful commitment, lack of information, wrong address, no recipient at the delivery address). These phrases are usually related to the commitment since the companies in question are in the service sector. Therefore, a logistics company warning of a problem with a delivery doesn't prompt any suspicion, peculiarly if the electronic mail contains some details of the situation.
- A demand to do something or face some consequence. For example, "collect your parcel inside 5 days otherwise it will be returned to the sender".
- Phrases about the content of an attachment or link (invoices, detailed data, documents).
- Phrases well-nigh the demand to do something (follow a link, open an attachment, print out a file, etc.).
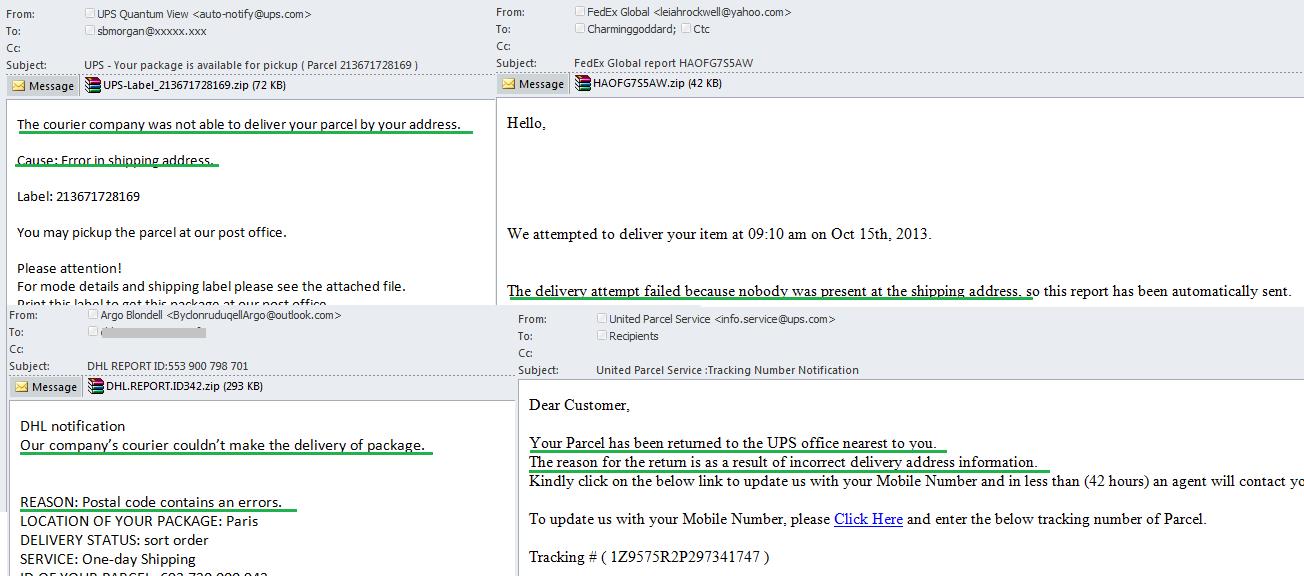
The scammers utilize deadlines like this to make recipients react immediately. The phishers hope that users will be so worried most losing the packet or paying actress costs that they won't hesitate to provide personal details or open up a suspicious attachment.

Users are unlikely to open up unknown attachments or follow unknown links. That's why scammers imitate official websites and present malware as a document with data a bundle. In addition, if the text of the notification states that the attachment contains, for instance, a assignment certificate, the malicious annal volition have a similar proper name, such as "consignment.zip." This applies to phishing links too – scammers proper name their links with an appropriate phrase from the text, such as "shipping information".
This uncomplicated trick is intended to reassure recipients that the attachment or link is perfectly legitimate.
Assuming the fraudsters have convinced the recipients that the electronic mail is existent, the side by side step is to tell the victims how to solve their problems. Fulfilling these instructions is the ultimate goal of the fraudulent email. Here it is important for the scammers not merely to tell recipients what they demand to practice, merely to brand them understand correctly what is written in the bulletin. To avert whatsoever misunderstanding on the role of the recipients, letters frequently contains detailed instructions virtually what to do.

How the text might change
Cheating the user is non the simply affair scammers have to do. They also need to bypass spam filters and deliver the email to the e-mail boxes of potential victims. One of the almost popular and long-used methods to featherbed filtering is to change text fragments within the email. Modern programs designed to transport out spam messages include ample opportunities to generate multiple changes in the text. The text of a bulletin which varies from e-mail to electronic mail makes the email unique, while dissimilar personal information specified inside one mailing (such as the number of the shipment, the class of the address, the dates) helps to convince recipients that the email is intended for them. In addition, the fraudsters can send out emails designed in the same style for several months – they merely demand to change some elements in the text.
Fraudulent notifications from delivery services tin can change:
- The information most the order/shipment, including the tracking number of the shipment, commitment dates, etc.)
- Contact details, sender names and company names. Some mass mailings provide an email address or a phone number of a company representative for feedback. This detail data changes from electronic mail to email. In addition, names of company representatives and fifty-fifty company names themselves may as well vary.
- The proper noun of the attachment. It mainly refers to malicious attachments which names vary in messages within ane mass mailing while these dissimilar names hide one and the same malicious programme.
- Links. In phishing emails and emails with malicious attachments scammers often specifically change the addresses of the links, masking them with the help of unlike URL shorteners. Near of these links are speedily blocked by current antivirus programs.
- Phrases indicating numbers and dates. These can refer to timetables (days, hours), sums of money and dates (day and month)
- The greeting. Here spammers more often than not use the electronic mail address and/or the name of the recipient. Sometimes they use generic expressions (Love client, Dear client, etc.) instead.
- Other text fragments. Some words are replaced with other phrases that have a similar meaning so the general sense of the sentence remains unchanged.
Allow'due south analyze some examples of changes in the text of fraudulent emails.
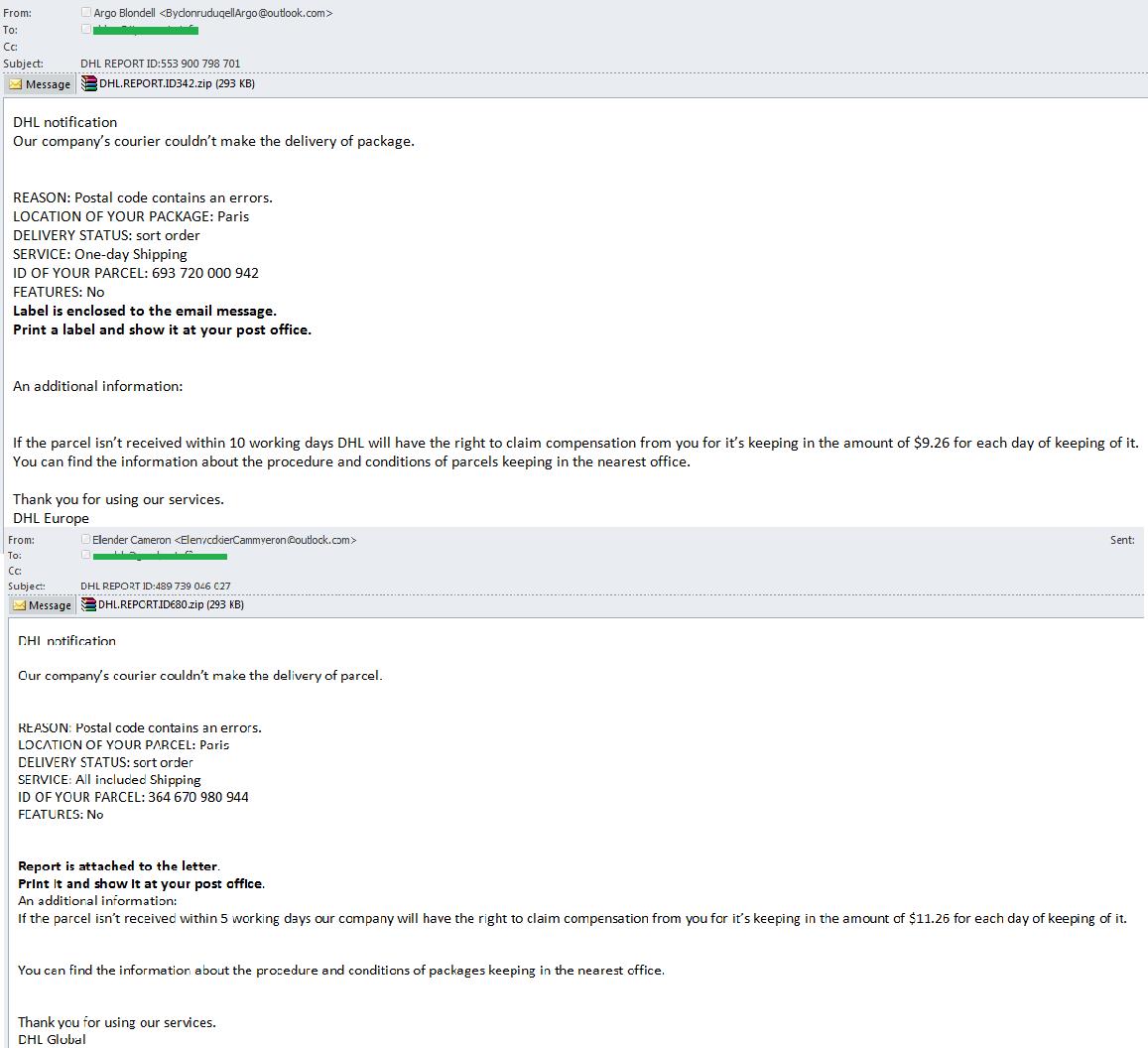
Below are some emails from still another mass mailing.
Fake pages
To steal personal information from users, scammers create phishing HTML pages which partially or completely re-create the official website of a company. If victims of fraud enters their personal information (banking concern details, usernames and passwords) on this folio, that data immediately falls into the fraudsters' easily.
To mask the links leading to phishing websites the fraudsters often use popular free URL shorteners. In addition, most services offer customers the ability to view the statistics on the curt link which tells fraudsters more virtually the number of clicks on whatever links etc. Phishing pages can be located on specially registered domains which normally take a brusk life span likewise equally on compromised domains whose owner may not fifty-fifty be enlightened that the spider web site is being used for fraudulent purposes.
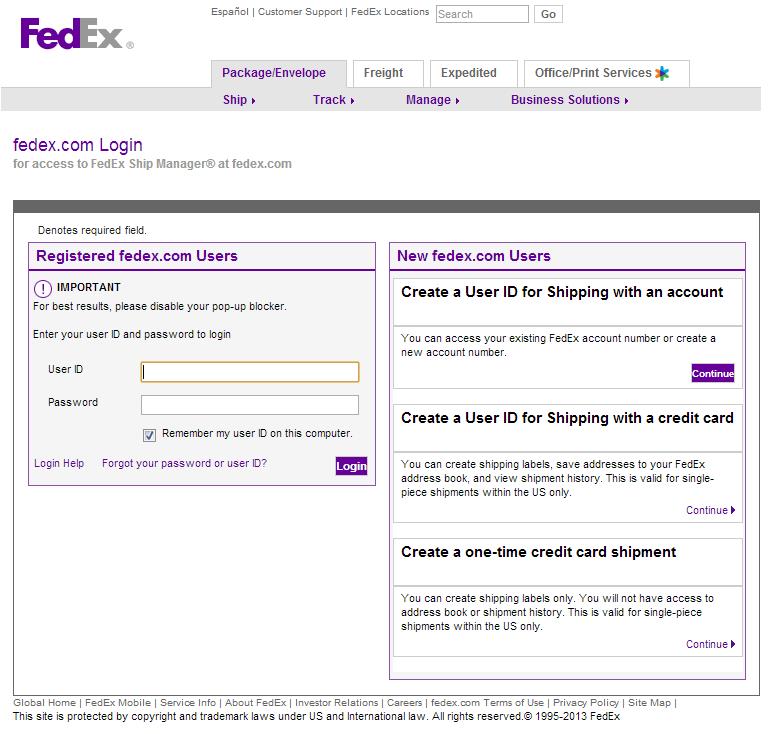
Permit'due south analyze a fake electronic mail sent on behalf of FedEx in which recipients are asked to update their business relationship data. The text of the e-mail contains a link to the official website of the visitor while the real accost to which the user is redirected is nothing like the legitimate page and is located on a free URL shortener service. This becomes obvious when you hover on the link.
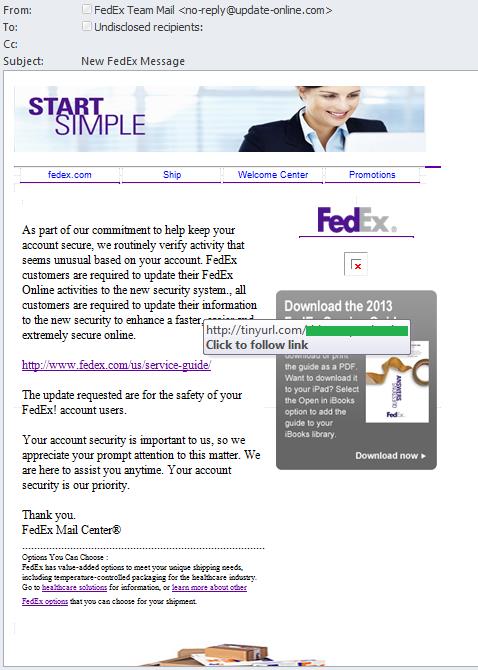
Afterward clicking the link, users get to a fraudulent folio imitating the official website of FedEx, where they are asked to enter their logins and passwords to access their accounts. One time the users fill in the fields and click "Login", the entered information is transmitted to the scammers who tin can so admission the victims' personal accounts. The menu tabs and other links on the phishing page are often inactive, then clicking on them will non take users to the appropriate folio. Nevertheless, in some cases, phishers imitate all links on the page and so that users do not have any dubiousness most its legitimacy. Sometimes the pattern of the page imitates the official site but does non copy it completely. If y'all have a closer wait at the details, you will see some differences between the designs of the existent and the imitation pages. Nonetheless, most users do not pay attention to small details and this abandon helps the scammers to steal personal data.
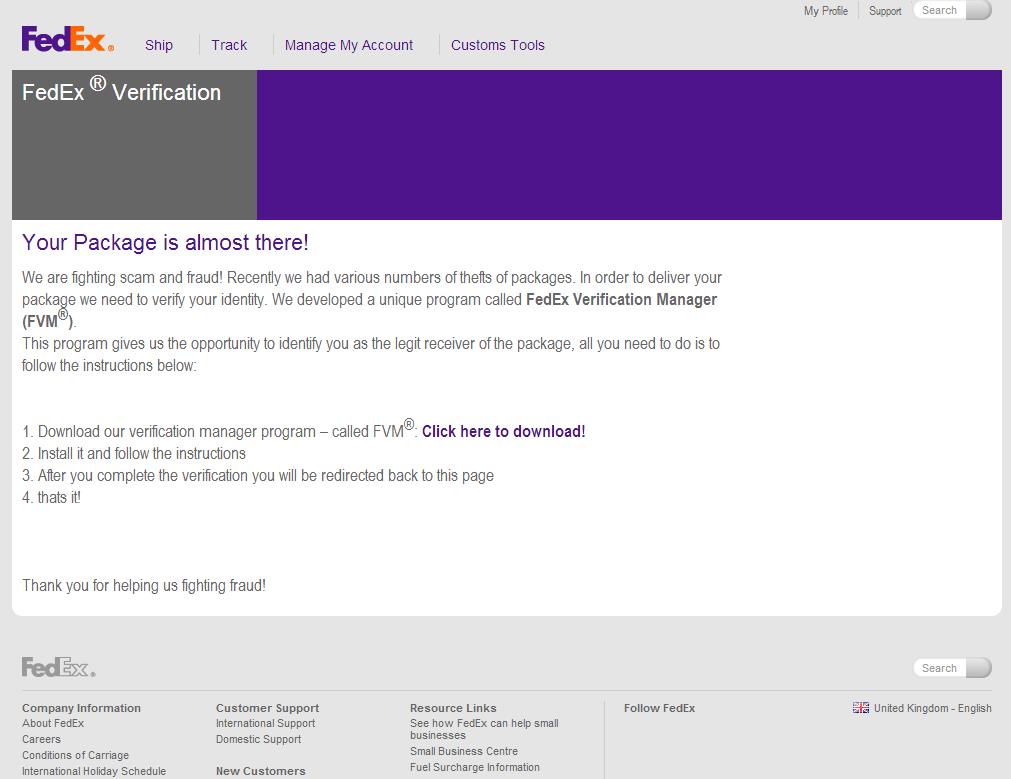
Below is yet another example of an email sent on behalf of FedEx. This time it contains a malicious link. The email informs recipients that delivery is impossible because of missing information. And now users accept to follow the specified link for verification.

The link leads to a fraudulent page where potential victims are invited to download a program that volition supposedly check whether they are actually going to receive a parcel. Naturally, the program turns to be the well-known Zeus Trojan, which helps the fraudsters to access the computer and all the personal information on information technology.
Scammers might non only include a phishing link in the body of the email, but likewise adhere an HTML phishing page designed to steal personal information. However this use of HTML attachments as phishing pages is unusual for fraudulent mailings sent on behalf of delivery services.
Fraudulent emails in different languages
To increment the audition of recipients and customers, spammers are mastering new languages. In improver to traditional English and High german, current spam traffic includes emails in Hebrew, Albanian and other languages which were found in advertising and fraudulent mailings a few years ago. For example, you may see simulated notifications from international delivery services written in Italian and Dutch. These emails practise not accept any special features that distinguish them from English- or German-language messages – to cheat users, the fraudsters resort to the same tricks.
For example, this Italian-language simulated notification from FedEx tells users to confirm their identity past following a fraudulent link.

Yet another mass mailing in Italian contained a malicious archive which included the Zeus/Zbot Trojan used to steal personal data. The fraudulent email claimed that the user profiles on the website had been updated and in that location was more than detailed information about information technology in the archive.
Another faux notification written in Dutch on behalf of TNT informs recipients that new accounts take been formed for them, with details in the attachment. The archive attached to the email contains Backdoor.Win32.Andromeda, a malicious file that allows the scammers to control the infected figurer without the user knowing.

Malware in fraudulent emails
Spam is 1 of the about popular ways of spreading malware and infecting computers on the Net. Attackers have various tricks to brand victims install malicious software on their computers. Email traffic includes a variety of private emails, such equally wedding ceremony invitations, dating offers and other similar messages. However, fake notifications from well-known companies and brands providing different services remain the near popular cybercriminal trick. International delivery services are too used by spammers every bit a comprehend for malicious spam.
Malware spread in fake notifications from commitment services is divided into:
- Trojan programs adult to perform unauthorized operations in society to delete, cake, change or copy data, to disrupt computer or network performance. Trojans distributed in spam include Backdoors, Trojan-Downloaders, Trojan-Proxies, Trojan-PSWs, Trojan-Spies, Trojan-Bankers and others
- Worms, malicious programs capable of unauthorized self-proliferation on computers or computer networks. Those copies go on to spread themselves further.
What is unsafe about malicious programs?
- They can steal usernames and passwords from users' accounts, as well equally fiscal or other data sought past the attackers.
- They can create botnets for distributing spam, DDoS attacks and other criminal activity
- They can provide fraudsters with control over victim computers, including the ability to run, delete or install any files or programs.
Current malicious programs integrate wide-ranging fraudulent functionality. In improver, some malicious programs can download other malware, providing additional opportunities. These might include stealing usernames and passwords entered in the browser or seizing remote control over the whole computer.
Malicious objects in fraudulent notifications tin be embedded directly in the email or downloaded from a link provided in the body of the message. The most dangerous affair about it is that malware can exist run and installed without users being aware or installing any software themselves. Typically, malicious ZIP (less often RAR) files enclosed in fraudulent emails have an executable .exe extension.
How to recognize phishing emails
Below are a number of features that can help to identify a fraudulent email.
- The sender address. If the sender address includes a random sequence of letters, words or numbers, or the domain has no connection with the official address of the company, the emails should undoubtedly be considered fraudulent and deleted without opening.
- Grammar and spelling mistakes. Wrong word order, wrong punctuation, grammer and spelling mistakes tin can also be a sign of a fraudulent mailing.
- Graphic design. Scammers are doing their best to make the email look very like to the original. To this ends they are trying to imitate other companies' corporate styles using some of their elements such every bit color schemes and logos. Inaccuracies and noticeable pattern errors are among the signs of a fake email.
- The content of the electronic mail. If the recipient of the email is asked under various pretexts to urgently provide or confirm personal data, download a file or a link – especially while being threatened with sanctions for not doing and so – the email may well be fraudulent.
- Links with dissimilar addresses. If the address of the link specified in the torso of the email and accost of the actual link to which you are redirected exercise not match, you are definitely looking at a fraudulent email. If you are viewing your email from the browser, the actual link can be normally seen in the bottom left of the browser window. If you use an email customer, the actual link can be displayed in a popup window if yous hover the cursor over the link in the text. Fraudulent links tin can also exist attached to a text phrase in the email.
- Attached archives. Generally, Zip and RAR athenaeum are used by cybercriminals to hide malicious executable EXE-files. Therefore, you should not open these archives or run the attached files.
- Lack of contacts for feedback. Legitimate emails always provide contact information for feedback – either the visitor or the sender's personal contacts.
- Form of address. Fraudulent emails practise not necessarily utilise the get-go proper name or the surname to address the recipient; sometimes a universal form of address ("client", etc.) is used.
Source: https://securelist.com/scammers-delivery-service-exclusively-dangerous/66515/
0 Response to "Fedex Express Delivery Service Email Scam Examples Review"
Post a Comment